Coinbase, the cryptocurrency exchange, announced a security bug in their API that would have allowed an attacker to take over user accounts. Coinbase halted all trading and withdrawals while they investigated the issue. The bug has since been fixed, and Coinbase has resumed trading.
The bug was found by a person who operates a twitter account under the name Tree of Alpha (@Tree_of_Alpha), quoting his twit “How a flaw in the new Advanced Trading feature would have allowed a malicious user to sell BTC or any other coin without owning them, and how Coinbase’s reaction speed on a Super Bowl Friday averted a possible crisis.”
Cryptocurrency exchange hacks
This bug is just the latest in a long line of cryptocurrency exchange hacks. In January, Coincheck was hacked for $530 million. In September, Bitfinex was hacked for $72 million. In December, ShapeShift was hacked for $200,000. And in February, Bithumb was hacked for $1.5 million.
These hacks are a reminder that cryptocurrency is still in its infancy, and that security is a major concern. In the future, as cryptocurrency becomes more mainstream, we can expect more secure exchanges and more secure wallets. But for now, we have to be careful and vigilant about where we store our cryptocurrency.
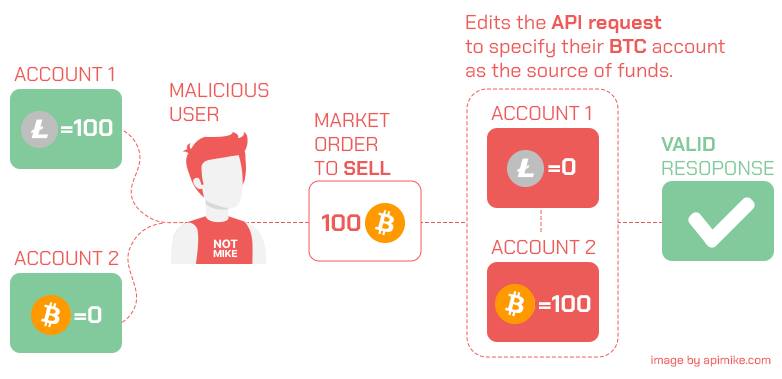
Broken object level authorization
Broken object level authorization is a security vulnerability that occurs when an application incorrectly authorizes user access to objects. In some cases, hackers can get their hands on sensitive data and resources that they should not have. When an application doesn’t properly check user permissions, this can allow them to do this.
This vulnerability can be exploited by an attacker who discovers a way to modify the application’s behavior. By changing the code of the application, an attacker can get around the security controls that are in place and get access to sensitive data that they shouldn’t have.
Broken object level authorization is a serious security vulnerability that can lead to a loss of data and other financial damage. It is important for businesses to make sure that their applications are safe from this vulnerability and that their security controls are strong enough.
Vulnerability Root Cause
“The underlying cause of the bug was a missing logic validation check in a retail brokerage API endpoint, which allowed a user to submit trades to a specific order book using a mismatched source account. This API is only utilized by our Retail Advanced Trading platform, which is currently in limited beta release. “
Coinbase
In conclusion
This article discusses a security vulnerability that was discovered on the Coinbase cryptocurrency exchange. The bug allowed an attacker to take over user accounts and caused the exchange to halt all trading and withdrawals. The bug has since been fixed, and Coinbase has resumed trading.
This article is a reminder that cryptocurrency is still in its infancy and that security is a major concern. In the future, as cryptocurrency becomes more mainstream, we can expect more secure exchanges and more secure wallets. But for now, we have to be careful and vigilant about where we store our cryptocurrency.
Post conclusion
Recently, I checked the API Security solution by BLST Security. They have a free open source tool and this line in their open-sourced CLI tool (Cherrybomb) is meant to generate a string parameter, either using a known set of values or using random ones.
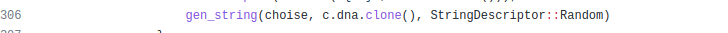
This exact line could have discovered the Coinbase API potential breach.